Consent of the governed of the government
Syed Rizwan Farook, the jihadist who killed 14 coworkers in San Bernardino last December, left behind a high-tech piece of evidence: his Apple iPhone. This simple piece of hardware has resulted in a court order compelling Apple to participate in unlocking Farook’s encrypted phone. This court order clearly oversteps the boundaries of the court’s power. While in the short term it seems like a good idea, allowing the government to force Apple to unlock the phone will cause damage in the long run.
Farook’s iPhone potentially contains a treasure trove of information, including a record of who he called in the days, weeks and months before he launched his heinous attack. This information could prove valuable in identifying his conspirators, many of whom are likely still at-large.
So the FBI is understandably very interested in extracting the information on Farook’s phone. The only problem? Apple’s security encryption is so sophisticated that even the FBI cannot crack it. To try to help, a federal court judge in California ordered Apple to assist the FBI in breaking the encryption and opening the phone.
Apple claims this order is not only illegal but also dangerous. If a backdoor is created, Apple argues, it compromises the security of all phones and can be used for improper purposes.
Thus the dilemma. On the one hand, the government has an interest in getting to the information on the phone. On the other hand, we all have an interest in the security that strong encryption provides.
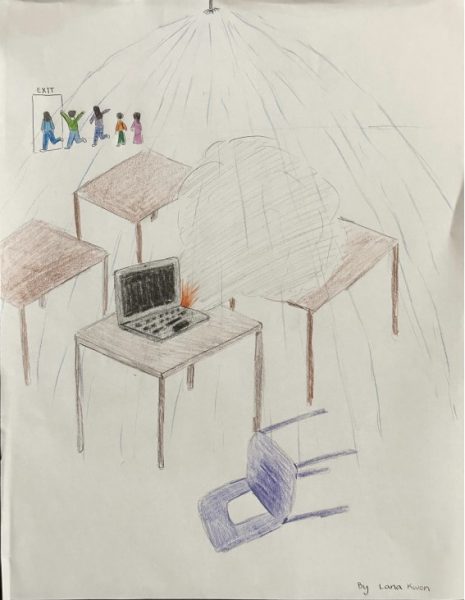
Apple should not be ordered to create code that does not currently exist to break the encryption. The fifth amendment currently provides that a court can issue a search warrant that allows law enforcement access to homes, offices and even safes. But the law does not give a court the power to force a company to spend weeks creating new software to help in an investigation.
The California court’s order, while well intentioned, is not supported by the law and is over-reaching by the court. By forcing Apple to create a backdoor that does not currently exist, the order also makes the phones less secure for millions of law-abiding Americans.
Finally, if the government believes that national security requires that phones have backdoors for law enforcement to gain entry, this is a policy issue that should be addressed by Congress (for example, by passing a law requiring backdoors), not by one judge in one court.
Your donation will support the student journalists of Woodbridge High School. Your contribution will allow us to purchase equipment and cover our annual website hosting costs.

Hello! My name is Nicholas and I am the Co-Editor-in-Chief of the Golden Arrow. This is my second year in journalism, and since last year I have discovered...